CDDC'23: Audio Steganography
This was a slightly more complex(more than usual for me) audio steganography challenge which required the use of least significant bits.
The Challenge
Along with this was a file, problem.wav.
Analysis
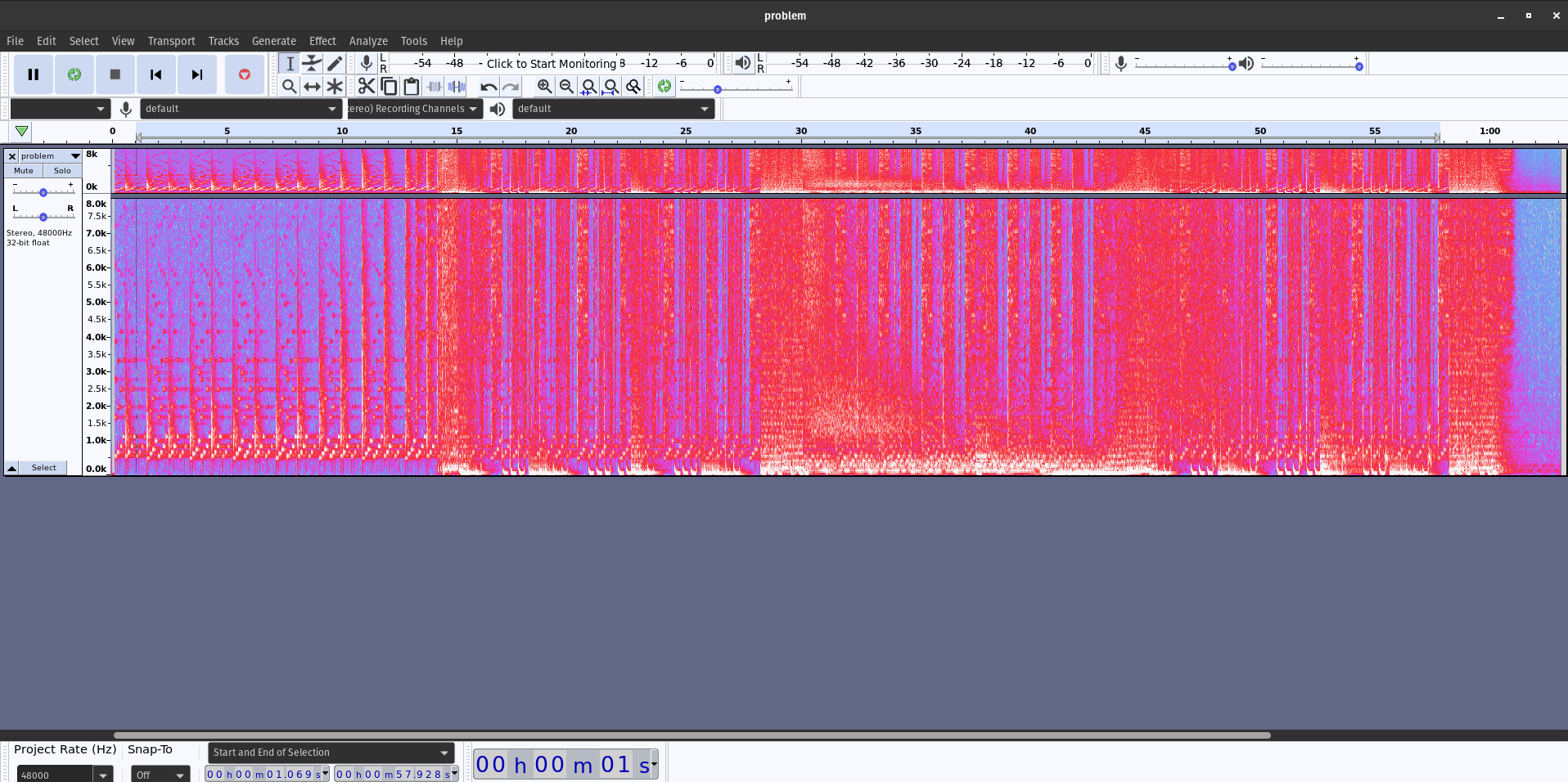
Usually, when tackling audio steganography challenges, I would use Audacity to view the spectrogram of the audio file. However, when taking a look at this (literally a) problem.wav, there didn’t seem to be anything I could get.
I had to look up other steganography methods, and found that a famous approach is using the Least Significant Bit algorithm, or LSB for short. It works by:
…substituting the least significant bit of each sampling point with a binary message
The Solution
I couldn’t find any online tool that gave an accurate result (or a result at all, actually), so I tried to write a Python script with reference to others’ in GitHub repos.
What I did was to:
- Open file in read-binary mode
- Read all audio frames and convert them to a byte array (list of bytes)
- Extract the LSB from each byte
- Convert binary data back to string
- Remove filler characters
This gave us the flag: CDDC2023{tH15_15_AuD10_5t39aNo9rAphy}!